Henan College of Arts and Culture, School of Cultural Communication, Zhengzhou, Henan Province,451464, China
Received: February 16, 2026
Accepted: March 27, 2026
Publication Date: April 25, 2026
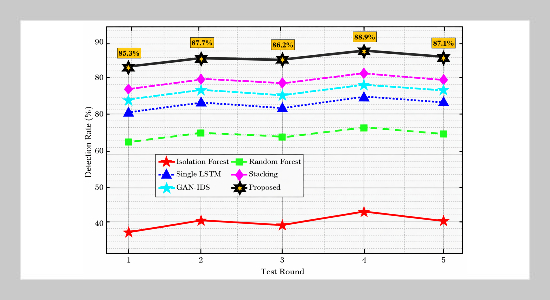
Detection performance of different models across five zero-day attack test rounds showing the stability of the proposed system
Copyright The Author(s). This is an open access article distributed under the terms of the Creative Commons Attribution License (CC BY 4.0), which permits unrestricted use, distribution, and reproduction in any medium, provided the original author and source are cited.
Download Citation: BibTeX | http://dx.doi.org/10.6180/jase.202609_32.013
Current network intrusion detection systems struggle with feature representation, unknown attack detection, and coordinated response. This paper proposes an intelligent system that fuses NetFlow and payload features, employs a three-level detection engine (deep autoencoder, Transformer, GNN), and integrates with software defined networking for real-time mitigation and adaptive feedback-driven model improvement. Experiments on amixed dataset combining the CIC-IDS2018 and UNSW-NB15 show a detection rate of 98.7%, a false positive rate of 0.86%, and an average detection rate of 87.04% for unknown attacks, with real-time interception success reaching 99%.
Keywords: Network Intrusion Detection and Prevention; Feature Fusion; Graph Neural Network; Software-Defined Network
- [1] N. Thockchom, M. M. Singh, and U. Nandi, (2023) “A novel ensemble learning-based model for network intrusion detection” Complex Intelligent Systems 9(5): 5693–5714. DOI: 10.1007/s40747-023-01013-7.
- [2] V. Ravi, T. D. Pham, and M. Alazab, (2023) “Deep learning-based network intrusion detection system for internet of medical things” IEEE Internet of Things Magazine 6(2): 50–54. DOI: 10.1109/IOTM.001.2300021.
- [3] N. S. Biyyapu, E. J. Veerapaneni, P. P. Surapaneni, S. S. Vellela, and R. Vatambeti, (2024) “Designing a modified feature aggregation model with hybrid sampling techniques for network intrusion detection” Cluster Computing 27(5): 5913–5931. DOI: 10.1007/s10586-024-04270-4.
- [4] M. Mohy-Eddine, A. Guezzaz, S. Benkirane, and M. Azrour, (2023) “An efficient network intrusion detection model for IoT security using K-NN classifier and feature selection” Multimedia Tools and Applications 82(15): 23615–23633. DOI: 10.1007/s11042-023-14795-2.
- [5] S. Sivamohan and S. S. Sridhar, (2023) “An optimized model for network intrusion detection systems in Industry 4.0 using XAI-based Bi-LSTM framework” Neural Computing and Applications 35(15): 11459–11475. DOI: 10.1007/s00521-023-08319-0.
- [6] V. Induru and P. N, (2019) “Enhanced network intrusion detection using long short-term memory for improved security analysis” International Journal of Engineering Technology Research Management 3(3): DOI: 10.5281/zenodo.15600702.
- [7] P. B. Udas, M. E. Karim, and K. S. Roy, (2022) “SPIDER: A shallow PCA-based network intrusion detection system with enhanced recurrent neural networks” Journal of King Saud University – Computer and Information Sciences 34(10): 10246–10272. DOI: 10.1016/j.jksuci.2022.10.019.
- [8] Z. K. Maseer, Q. K. Kadhim, B. Al-Bander, et al., (2024) “Meta-analysis and systematic review for anomaly network intrusion detection systems: detection methods, datasets, validation methodology, and challenges” IET Networks 13(5–6): 339–376. DOI: 10.1049/ntw2.12128.
- [9] W. Zhao and Z. Zhao, (2024) “Providing a hybrid approach to increase the accuracy of intrusion detection systems in computer networks” Journal of Engineering and Applied Science 71(1): 123. DOI: 10.1186/s44147-024-00404-y.
- [10] G. Apruzzese, L. Pajola, and M. Conti, (2022) “The cross-evaluation of machine learning-based network intrusion detection systems” IEEE Transactions on Network and Service Management 19(4): 5152–5169. DOI: 10.1109/TNSM.2022.3204615.
- [11] M. Rashid, J. Kamruzzaman, T. Imam, et al., (2022) “A tree-based stacking ensemble technique with feature selection for network intrusion detection” Applied Intelligence 52(9): 9768–9781. DOI: 10.1007/s10489-021-02968-1.
- [12] M. Maddu and Y. N. Rao, (2024) “Network intrusion detection and mitigation in SDN using deep learning models” International Journal of Information Security 23(2): 849–862. DOI: 10.1007/s10207-023-00771-2.
- [13] S. Mohamed and R. Ejbali, (2023) “Deep SARSA-based reinforcement learning approach for anomaly network intrusion detection system” International Journal of Information Security 22(1): 235–247. DOI: 10.1007/s10207-022-00641-0.
- [14] V. Ravi, T. D. Pham, and M. Alazab, (2023) “Deep learning-based network intrusion detection system for Internet of Medical Things” IEEE Internet of Things Magazine 6(2): 50–54. DOI: 10.1109/IOTM.001.2200183.
- [15] M. Ali, M. Haque, M. H. Durad, A. Usman, S. M. Mohsin, H. Mujlid, et al., (2023) “Effective network intrusion detection using stacking-based ensemble approach” International Journal of Information Security 22(6): 1781–1798. DOI: 10.1007/s10207-023-00718-7.
- [16] P. Barnard, N. Marchetti, and L. A. DaSilva, (2022) “Robust network intrusion detection through explainable artificial intelligence (XAI)” IEEE Networking Letters 4(3): 167–171. DOI: 10.1109/LNET.2022.3186589.
- [17] M. Mehmood, T. Javed, J. Nebhen, et al., (2022) “A hybrid approach for network intrusion detection” CMC–Computers, Materials Continua 70(1): 91–107. DOI: 10.32604/cmc.2024.054966.
- [18] S. Das, S. Saha, A. T. Priyoti, et al., (2021) “Network intrusion detection and comparative analysis using ensemble machine learning and feature selection” IEEE Transactions on Network and Service Management 19(4): 4821–4833. DOI: 10.1109/TNSM.2021.3138457.
- [19] R. Ghanbarzadeh, A. Hosseinalipour, and A. Ghaffari, (2023) “A novel network intrusion detection method based on metaheuristic optimisation algorithms” Journal of Ambient Intelligence and Humanized Computing 14(6): 7575–7592. DOI: 10.12652/s12652-023-04571-3.
- [20] Y. S. Almutairi, B. Alhazmi, and A. A. Munshi, (2022) “Network intrusion detection using machine learning techniques” Advances in Science and Technology Research Journal 16(3): 193–206. DOI: 10.12913/22998624/149934.
- [21] S. S. Md, (2024) “A comparative analysis of network intrusion detection using artificial intelligence techniques for increased network security” International Journal 13(2): 4014–4025. DOI: 10.30574/ijsra.2024.13.2.2664.
- [22] I. Ortega-Fernandez, M. Sestelo, J. C. Burguillo, et al., (2024) “Network intrusion detection system for DDoS attacks in ICS using deep autoencoders” Wireless Networks 30(6): 5059–5075. DOI: 10.1007/s11276-022-03214-3.
- [23] C. Park, J. Lee, Y. Kim, et al., (2022) “An enhanced AI-based network intrusion detection system using generative adversarial networks” IEEE Internet of Things Journal 10(3): 2330–2345. DOI: 10.1109/JIOT.2022.3211346.
- [24] M. Amru, R. J. Kannan, E. N. Ganesh, et al., (2024) “Network intrusion detection system by applying ensemble model for smart home” International Journal of Electrical and Computer Engineering 14(3): 3485–3494. DOI: 10.1159/ijece.v14i3.pp3485-3494.
- [25] K. He, D. D. Kim, and M. R. Asghar, (2023) “Adver sarial machine learning for network intrusion detection systems: A comprehensive survey” IEEE Communications Surveys Tutorials 25(1): 538–566. DOI: 10.1109/COMST.2022.3233793.